Technical Demo
Book a Technical Demo
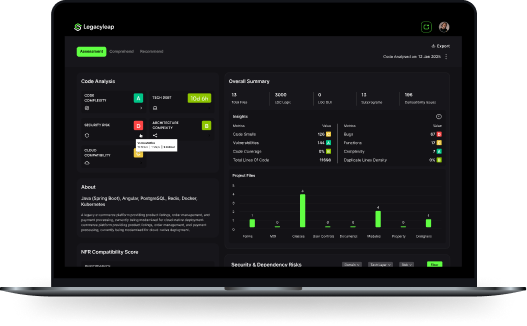
Explore how Legacyleap’s Gen AI agents analyze, refactor, and modernize your legacy applications, at unparalleled velocity.
"Ten years," Kael whispered, a grin spreading across his face. He felt like a god. He generated another. And another. He began posting them to the boards under his alias, Void_Walker . The community went wild. The ThumperTM was real.
Suddenly, his webcam light flickered on—a steady, unblinking green eye. A window popped up, but it wasn't from AVG. It was a terminal window, scrolling text at a blinding speed. Avginternetsecurity2017 key thumpertm
The program didn’t look like a standard keygen. Instead of a random string of alphanumeric characters, a visualizer appeared—a simple, rhythmic wave moving across the screen. Thump. Thump. Thump. It sounded like a heavy bass drum through his headphones. "Ten years," Kael whispered, a grin spreading across
The room went silent. The neon hum was gone. Kael sat in the dark, realizing that in the world of 2017 security, the most dangerous threat wasn't the virus—it was the guy who thought he’d found the cure for free. And another
Kael realized too late that the ThumperTM wasn't a key generator. It was a Trojan. By "thumping" the AVG servers, he hadn't been breaking in; he had been creating a two-way harmonic tunnel. He was the distraction—the loud noise that covered the sound of a much bigger heist.
The neon hum of the "Undercroft" was the only thing keeping Kael awake. In the digital purgatory of 2017, where the line between script kiddie and cyber-warlord was drawn in stolen credit card numbers and expired software licenses, Kael was a scavenger. He didn't build; he cracked.